Financial highlights
Last trade 50.87€
Variation -2.81%
03/06/2026 - 05:39 PM
data source: Investis Digital
Financial highlights
Last trade 50.87€
Variation -2.81%
03/06/2026 - 05:39 PM
data source: Investis Digital
Financial Results & Reports
Press releases
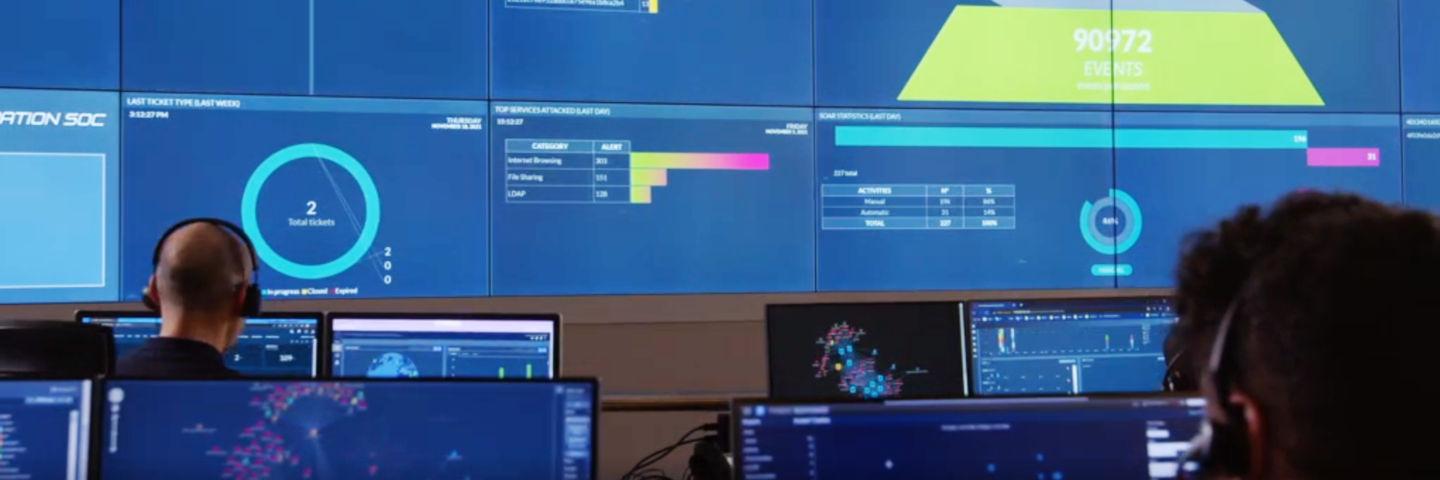
Cyberwarfare described day by day by analysts at the SOC in Chieti: from the first attacks against 50 Ukrainian government offices to the response of Anonymous and other hacktivist groups in support of Zelensky’s government. Aldo Sebastiani: “Leonardo is committed to protecting vital organisations, in Italy and beyond”
The conflict between Russia and Ukraine is also being fought behind the scenes on the Internet. Cyber networks have set the stage for a different kind of war, waged by hacker groups, secret service specialists and the defence structures of the nations involved. Governments, ministries, banks, industries, state media – the targets are manifold, as are the traces of this unfolding conflict that are emerging on social networks.
Analysts at the SOC in Chieti, home to Leonardo’s cyber security activities, are currently monitoring an enormous quantity of incidents related to the Russian-Ukrainian conflict. While raids by cyber attackers allegedly traceable to the Kremlin have been taking place for months, ever since Putin ordered a ‘physical’ attack, groups of hackers and hacktivists have come out in support of Ukraine. The goal in this case are crucial websites, media, and the critical infrastructure of Russia and its neighbouring countries.
The latest report, issued on 1 March at 13:19, concerns the ‘YourAnonNewsIT’ group, which has posted a tweet claiming to be in possession of tens of thousands of Russian passwords, without however specifying the entities involved.
— YourAnonNewsIT (@YourAnonNewsIT1) March 1, 2022
Yet this is only the latest in a long series of claims assessed by the analysts in Chieti. “Leonardo is committed to protecting vital organisations, in Italy and beyond,” explained Aldo Sebastiani, director of the SOC in Chieti. “The current Ukrainian crisis shows just how important cyber security has become. Cyber security is a multi-disciplinary subject that relies on cooperation, and this war has proven the increasing importance of having professional experts with an overall vision of geopolitics, technology, law and process governance.”
The first signs of the crisis that later erupted on 24 February date back to the first half of January. The hybrid war began at least 45 days before the physical war. “DDoS and defacement attacks have targeted critical infrastructure, government and finance bodies on Ukrainian soil,” states the SOC report ‘Evolution of the Russian-Ukrainian Threat’. On the eve of the military offensive, attacks on the cyber front escalated: “Destructive activities linked to sabotage operations began on 23 February 2022 with the dissemination of a wiper. The main goal of this type of malware is to delete all the data stored on target devices,” states the report.
A cyber war, consisting of a powerful distributed denial-of-service (DDoS) attack on the websites of certain Ukrainian government agencies, was the precursor to the first air strikes in the early hours of 24 February. In particular, the targets of this cyber-attack were the Ukrainian Verkhovna Rada Parliament, the Council of Ministers and the Ministry of Foreign Affairs. In total, it is believed that about 50 government sites were involved.
The cyber weapon used against Ukraine is a malware known as the Hermetic Wiper, detected following a number of incidents involving Ukrainian government websites and banks. Meanwhile, as Russian forces crossed the Ukrainian borders, further attacks caused the websites of the Ukrainian Ministry of Foreign Affairs, Cabinet of Ministers and Rada Parliament to crash.
On the same day, a new sandworm malware named Cyclops Blink, used by Russian threat actor Sandworm (also known as Voodoo Bear), was identified by the United Kingdom's National Cyber Security Centre (NCSC), the Cybersecurity and Infrastructure Security Agency (CISA), the National Security Agency (NSA), and the Federal Bureau of Investigation (FBI). Although there is currently no way of linking the Cyclops Blink threat directly to the current crisis between Russia and Ukraine, one cannot exclude the possibility that it may be used in the future to conduct targeted attacks on critical infrastructure beyond Ukrainian territory.
The well-known hacktivist group Anonymous has officially sided with Ukraine on its Twitter profile. The collective is following the conflict closely, publishing posts in which it claims to have attacked several Russian government websites and ISP providers, which are currently offline.
— Anonymous (@YourAnonNews) February 24, 2022
Phishing campaigns by the ‘UNC1151’ group have been detected targeting private 'i.ua' and 'meta.ua' accounts of Ukrainian military personnel and citizens. UNC1151, believed to be linked to the Belarusian Government and involved in the Ghostwriter campaign, has been conducting disinformation campaigns in line with Russian interests since March 2017. In the past, its operations had mainly targeted audiences in Lithuania, Latvia and Poland and promoted narratives critical of NATO’s presence in Eastern Europe.
Reports of widespread phishing of https://t.co/BKfr6z5N3W and https://t.co/OZpQWYRCz4 accounts (e.g. personal accounts of Ukrainian citizens) by UNC1151 (Belarusian Military). https://t.co/Rzf82yRjja
— Ben Read (@bread08) February 25, 2022
A Twitter profile thought to be linked to Anonymous claims to have breached and leaked around 200GB of emails from Belarusian weapons manufacturer Tetraedr, which the collective claims provided Russia with logistical support in its invasion of Ukraine.
JUST IN: Hacktivist group #Anonymous has successfully breached and leaked about 200GB of emails from Belarusian weapons manufacturer Tetraedr. This company has provided Vladimir Putin with logistical support in his invasion of #Ukraine. #OpRussia #StandWithUkriane pic.twitter.com/3MhSbrggbh
— Anonymous TV 🇺🇦 (@YourAnonTV) February 26, 2022
A tweet reports news of a DDoS attack on the website of the Russian space agency Roscosmos. The attack was allegedly organised from the Ukrainian city of Lviv and carried out with the aid of botnets located on servers in various parts of the world. The website is now back online.
Moscou, 26 février. Une attaque DDoS contre le site web de #Roskosmos a été menée depuis #Lviv (Ukraine) à l'aide d'un réseau de bots. C'est ce qu'a rapporté le service de presse de l'organisation.
— SoHan Sun (@SunSohan) February 26, 2022
Le problème a été rapidement résolu. pic.twitter.com/f2eM1bXp24
NetBlocks metrics confirm the restriction of Twitter in Russia. Access to the platform and back-end servers has been restricted to major networks, including Rostelecom, MTS, Beeline and MegaFon, since 09:00 on Saturday, 26 February.
⚠️ Confirmed: Live metrics show that Twitter has been restricted on multiple providers in #Russia as of 9:00 a.m. UTC; the incident comes as the government clashes with social media platforms over policy in relation to the #Ukraine conflict 📉
— NetBlocks (@netblocks) February 26, 2022
📰 Report: https://t.co/ihPX8fb86s pic.twitter.com/nGrcHzjIXd
According to information shared by CERT-UA, the company Proofpoint has detected a phishing campaign targeting ukr[.]net accounts of Ukrainian military personnel and carried out through a malicious Excel document containing a vba macro.
Ukraine’s Deputy Prime Minister, Mykhailo Fedorov, has posted a tweet saying that Ukraine is creating an IT army in order to fight the conflict also on the cyber front.
We are creating an IT army. We need digital talents. All operational tasks will be given here: https://t.co/Ie4ESfxoSn. There will be tasks for everyone. We continue to fight on the cyber front. The first task is on the channel for cyber specialists.
— Mykhailo Fedorov (@FedorovMykhailo) February 26, 2022
A constantly updated list of the threat actors currently involved in the war between Russia and Ukraine has been published. The information provided includes the country supported and the attack methods used – and observed – so far.
📢Updated list of #cyber groups involved in #UkraineRussiaWar - real time updates here and daily list update below. New groups in yellow.
— CyberKnow (@Cyberknow20) February 28, 2022
Larger project starting soon. #cybersecurity #threatintelligence #infosec #CyberAttack #Cyberwar @xxNB65 https://t.co/xduzATcGNE pic.twitter.com/tIeKYymKOc
Anonymous has posted a tweet stating that it has taken down the website of the Belarusian Ministry of Defence.
TANGO DOWN - Belarus Military https://t.co/uyflfYsXHQ pic.twitter.com/aBSNRV9CX1
— Anonymous (@YourAnonNews) February 27, 2022
Moreover, a tweet published by Against The West states that Anonymous has joined them in their operations hitting Russian businesses operating in the transport sector. In particular, Yakutiya's ferry service has been taken offline.
Anonymous have joined us in beginning our sub operation hitting transportation industries within Russia. First, Yakutiya's ferry service is offline. Data stole and deleted #Ukraine #AgainstTheWest #Anonymous pic.twitter.com/bbJpAGzK4p
— ATW 🇺🇦 🇪🇺 (@AgainstTheWest_) February 28, 2022
2026-06-04T02:36:29Z
cookie_disclaimer:true
page_disclaimer :false